Governance and Data Safeguards
Last Updated: March 17, 2026. This document outlines how Seoul Data Partners manages personal information within our B2B intelligence framework in Malaysia.
Information Collection Protocols
In the course of establishing professional partnerships, Seoul Data Partners collects specific data points essential for operational efficiency and cross-border intelligence sharing. We categorize this data into two primary streams:
Direct Engagement
Information provided during partner onboarding, inquiry forms, and strategic consultations, including names, corporate contact details, and professional credentials.
Technical Telemetry
Automated collection of IP addresses, browser types, and engagement patterns to optimize our digital hub for enterprise-grade performance.
We do not engage in broad-spectrum data harvesting. Collection is strictly limited to information that facilitates B2B interaction within the Malaysian regulatory framework, including the Personal Data Protection Act 2010 (PDPA).
Strategic Utilization
Data serves as the foundational layer for our intelligence services. We process information for the primary purpose of maintaining the Partner Hub ecosystem and delivering tailored B2B insights. Specific usage includes:
- Optimization: Analyzing hub traffic to improve the delivery of strategic intelligence artifacts.
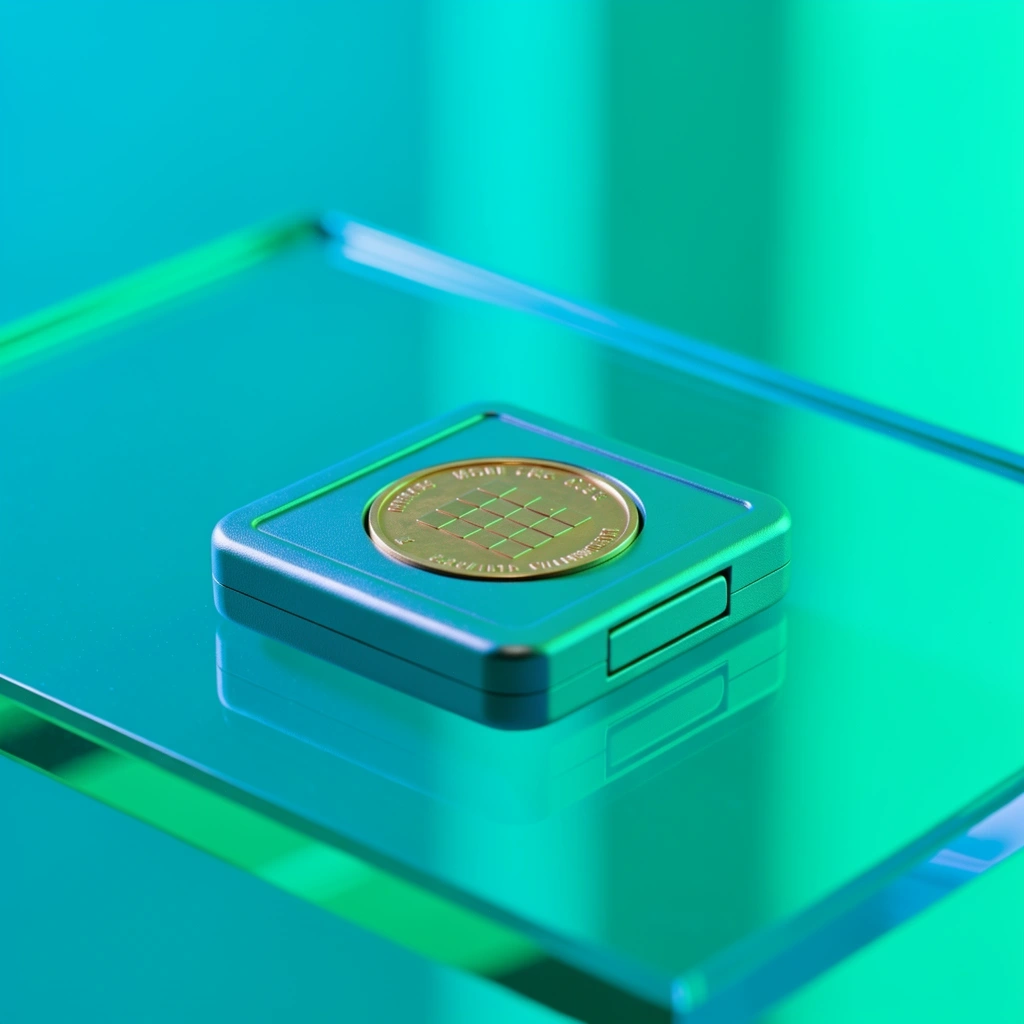
- Compliance: Fulfilling auditing requirements and visual identity verification for institutional members.

Partnership Exchange & Disclosure
Seoul Data Partners does not sell personal information to third-party marketers. Information exchange is strictly governed by institutional agreements. We may share data under the following circumstances:
- With your explicit consent for specific B2B introductions.
- To professional service providers who assist in our operational security.
- When required by Malaysian law or to protect the data integrity of our hub.
- During corporate transitions, such as mergers or consolidations within the hub's structure.
Security Integrity
We implement enterprise-grade encryption and access controls to protect sensitive information from unauthorized access or alteration. Our internal protocols include:
Encrypted Transmissions
All external-facing portals use TLS 1.3 or higher.
Least-Privilege Access
Internal data access is restricted on a "need-to-know" basis.
Individual Rights
Under Malaysian data protection standards, you maintain the right to:
Explore our legal framework in full.
Understand the terms governing our intelligence exchange and how we handle specialized web technologies.